WordPress Security Series – Part 2
Even with protective measures in place you need tools that help identify when a malicious bot or virus compromises your site. Part 2 of 3 part series.

Truly securing your website requires that you consider and address all three components of a complete security strategy — protection, detection, and recovery. No matter how good your website protection is, hackers may find a way to infiltrate your site. It does no good to implement protective measures and then not be able to identify when a malicious bot or virus compromises your site.
The majority of hacks today are not obvious. They can result in websites becoming infected and then spreading that infection to unaware users and possibly even other servers. How can you tell if your website has been hacked before it gets out of control? More importantly, how can you identify whether your website has been hacked before your customers do? In this Part 2 of our 3-part series, we will identify ways to detect whether your site has become a victim of hackers.
Your Site Is Offline
An obvious sign is that your site is not available — you get an internal server error or see your URL presenting your hosting company’s default “Coming Soon” page. If your hacked site is sending spam email or consuming massive server resources, your hosting provider will likely take your site offline. This can be disastrous. It means that your site has been infected long enough for hackers to do serious damage and, more importantly, loss of business and lost revenue.
Google Flags Your Site
If your application has been compromised and is actively spreading malware, chances are other security tools have picked up on it. Google will check for problems when it scans your site and will report back any problems found in Google Search Console (formerly called Google Webmaster Tools). Unfortunately, while Google is very good at telling you about problems, it is also very good at letting your customers know as well.
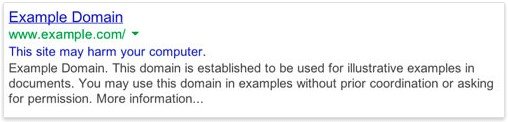
Google often simply removes hacked sites from search results, but in some cases, a site may still be listed and flagged with a message indicating “This site may be hacked” or “This site may harm your computer.”
“This site may be hacked” means that Google detected something out of the ordinary on the site, such as unusual changes to existing pages or adding new ones with SEO spam or redirects. These sites do not typically display the standard Google malware warning page.
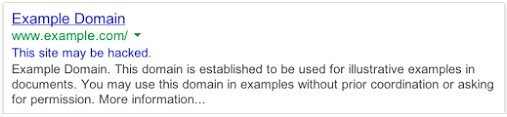
“This site may harm your computer” means that Google has detected malware on the site and if you visit it, you do so at your own risk. If using the Chrome browser, you will see the Google malware warning when you click through — an alert indicating that the site is currently unsafe for your operating system.
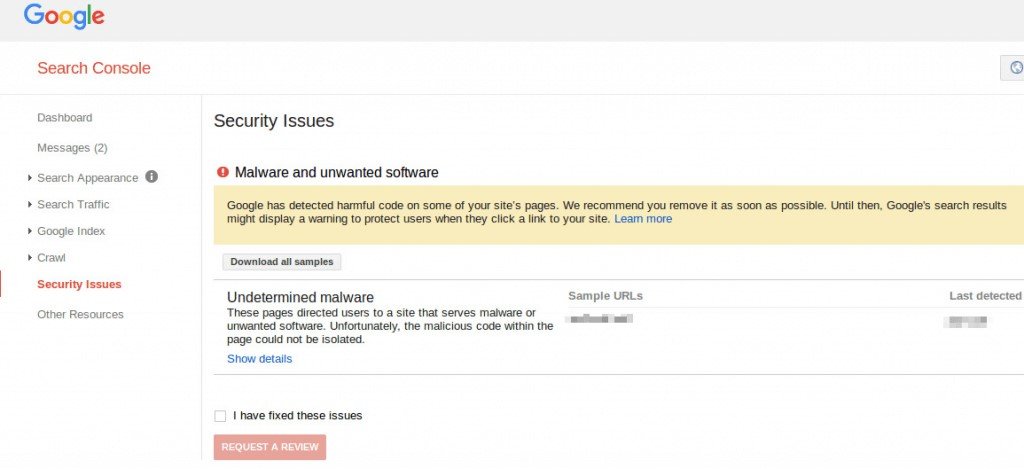
Google’s Search Console Identifies Malware
If you have a website, you should set up Google Search Console. It will alert you to any problems Google encounters when indexing your site. It can be configured to proactively email you alerts when a scan detects that your site is infected with malware. Early notification may allow you to correct issues before Google starts listing your site as flagged.
You Notice Unusual Activity on Your Site
Another major indicator your site has been hacked is unusual activity. This is often in the form of excessive amounts of spam or traffic spikes. If you are actively blogging, for example, and you have an old post that suddenly becomes popular for no apparent reason, you may have a problem.
Keep an eye out for site visitors from non-typical locations. An increase in traffic from China on a site that provides U.S. government contracting services would likely be a bad sign. As a general rule of thumb, increased foreign traffic tends to be the biggest indicator of a potential problem or a site under attack from hackers. Monitor your Google Analytics account and your site’s administrative dashboard for unexplained usage patterns. If anything looks suspicious, be sure to investigate as quickly as possible.
Your Site Is Not Doing What It Was Designed To Do
Monitoring your website is the single best way to notice when something suspicious is occurring. Pages are displayed unexpectedly or are redirecting visitors to an unrelated page. Popup windows just won’t stop. Your site now takes significantly longer to render page results than it used to. Network traffic has increased but there have been no marketing campaigns to explain the surge. A small online commerce site that normally sees about 20 orders a day, for example, should question a day with thousands of orders.
These are not always indicators that a site has been compromised by a hacker, but it’s always better to investigate something askew as soon as possible rather than waiting for a major disturbance. If your site is not functioning as expected, find out why. Is a malicious ad taking control of your page functionality? Has the code on your page been modified yet no changes have been made by your development team? Have your visitor accounts or databases been tampered with? Be sure to regularly interact with your website and familiarize yourself with overall data features and functionality so that unexpected behavior can be immediately identified for investigation.
No matter how your website was built or managed, some common signs of a hacked site are listed below.
- Displaying popups that you didn’t implement
- Displaying odd text in your footer or in the View Source window
- Linking to other sites or auto-linking keywords when you didn’t create links
- Showing obfuscated or encoded text in plug-ins
- Redirecting, immediately or after a short length of time, to another URL
- Logging of unusual activity or showing spikes in traffic or bandwidth usage
You Find Suspicious Log Messages
When set up correctly, logs can be a gold mine of hacker attack information. If database logs show unexpected queries and multiple errors in a short period of time, that may be a sign someone is poking around your site looking for — or has already found — a SQL injection vulnerability. Your web server can log inbound and outbound network connections through system FTP and HTTP logs. Those logs can pick up warning signs of unauthorized or malicious activity. Web servers should generally only initiate connections with internal databases. If your logs indicate there are outbound network connections from your webserver to public IP addresses and computer systems, you should be asking why.
You should not, however, only be focused on what’s moving outside the network. If your web server is communicating with other internal network resources such as shared user files and individual user computers, that can be a sign that hackers have gained entry and are sniffing around your network. If your site allows users to upload files, you should ensure that it uses a file server not connected with your enterprise systems.
Web applications should also log when administrators are accessing the site and you should verify what these accounts are doing. Check regularly for visitation from unexpected locations and off-hour site access. Unexplained instances of web administrator account access are typically a strong sign of an attack or true security breach.
You Are Surprised by New Processes, Users, or Jobs
Regularly monitor the processes running on your web server so you can detect when an unknown process is spawned, a known process runs at an unusual time, or over consumes server resources. An unknown process is generally a pretty big clue that you no longer have total control of your website.
Once a hacker has an account on your server, there is little they can’t do. Regularly monitor your site for new visitors, especially those with administrative privileges. Those accounts are not typically created on the fly, so it’s worth following up whenever such an account is created. If users who don’t require elevated privileges or root access are suddenly making access requests, you may likely be under attack from a hacker using stolen credentials. Simple solutions to situations like this include multi factor authentication and frequent updates to login credentials.
Another common trick used by hackers is to schedule a background task that will re‑infect your site or perform some other malicious activity after you conduct a cleanup. Be sure to look at the cron jobs on your server or in your hosting environment to make certain there are no jobs scheduled that you were not aware of or that you did not set up. This is an easy check with most commercial hosting providers via the cron scheduler in cPanel or other control panel dashboard used by your host. If you have your own server, you should periodically check crontab to ensure all is well.
Files Have Changed or They Are Mysteriously Multiplying
Do the timestamps on your web files indicate that files you last changed years ago have recently been updated? If your web server wasn’t correctly configured or your application has a vulnerability, hackers can modify your application to run their own malicious code. Check timestamps to ensure your data files aren’t being modified without authorization, and if they have been, compare those data files against earlier versions to identify what has changed. If your application uses third-party plugins, be sure to check that these data files aren’t getting updated or installed without warning. Prior to installation, exercise due diligence and research to ensure any plugin used won’t add malicious functionality to your website.
In addition to changing data files, ensure that you do not have a lot of new files on your web server that can’t be accounted for. New files showing up at the root of your site is a problem, especially if they are scripts or other types of executable files. If you find unexplained files in your webroot or elsewhere on your server, you have a breach. Adding files to webroot should never be a surprise and always be well-documented.
Related Posts

About the Author
Lisa is the Chief Revenue Officer at Smart Solutions, with over 35 years of experience developing custom software, eCommerce solutions, and business applications across commercial and government sectors. She leads strategic direction for growth, including product and service alignment and customer experience. Lisa works closely with internal teams to ensure initiatives support business objectives and long-term client success.Explore More Resources
Make the Right Next Decision
If performance has plateaued, complexity is increasing, or prior investments aren’t delivering as expected, we evaluate what’s working, where efforts are misaligned with business goals, and partner with your team to advance initiatives that drive measurable progress.










